Our Red Team Techniques

Phishing Simulations
Utilizing realistic phishing tactics to assess how well your employees can detect and respond to fraudulent attempts.
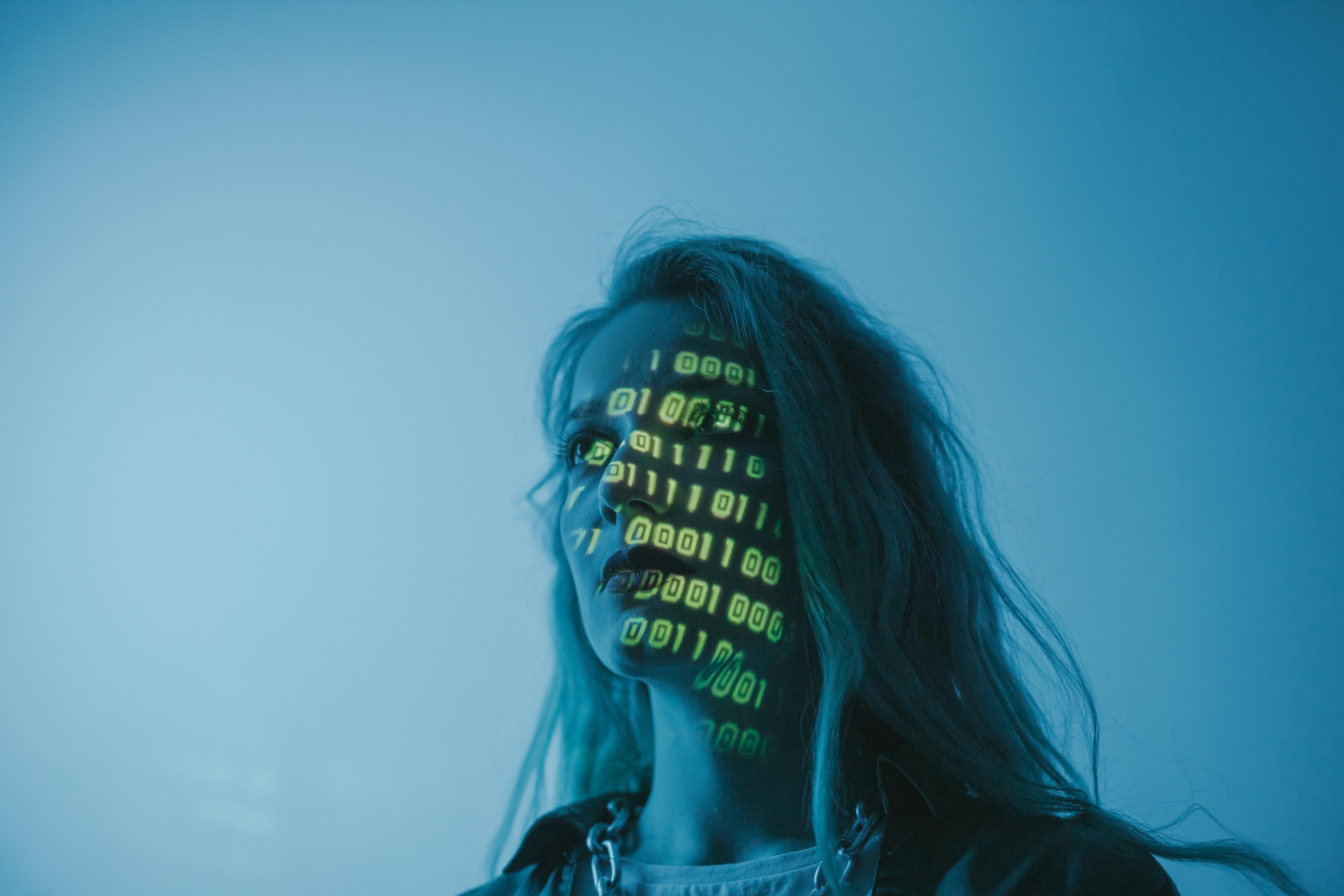
Social Engineering Tactics
Testing the human element of your organization through social engineering, aiming to discover vulnerabilities in people's awareness and procedures.

Physical Intrusions
Simulating unauthorized physical access to test the effectiveness of your physical security measures.

Network Penetration Testing
Conducting comprehensive analyses of your network defenses to identify exploitable vulnerabilities and gaps.

Vulnerability Assessments
Performing thorough examinations of your systems and applications to highlight weaknesses before attackers can exploit them.

Reporting & Recommendations
Providing detailed reports on findings, along with actionable recommendations to enhance your security posture.